Most of our readers will be familiar with security researcher Troy Hunt's password breach project 'haveibeenpwned', a simple explanation is that it hosts a database of password breaches which can be searched for exposure. If your company or organisation has suffered from a hacking incident then there's a reasonable chance that any credentials or hashes retrieved will be sold or traded onwards to other would be threat actors, and hopefully a copy finds its way to HIBP at some point. The news this week is that the project will transition from a solo effort to an open source project (URL) which should ensure its long term value as one of the tools available for security researchers, individuals and the cyber community as a whole to understand potential exposure.
One disappointing revelation from HIBP is how often individuals reuse their passwords across accounts against all security best practices. This of course means that a breach in one account can lead to the breach of multiple other accounts particularly if users persist with the same passwords over an extended period of time.
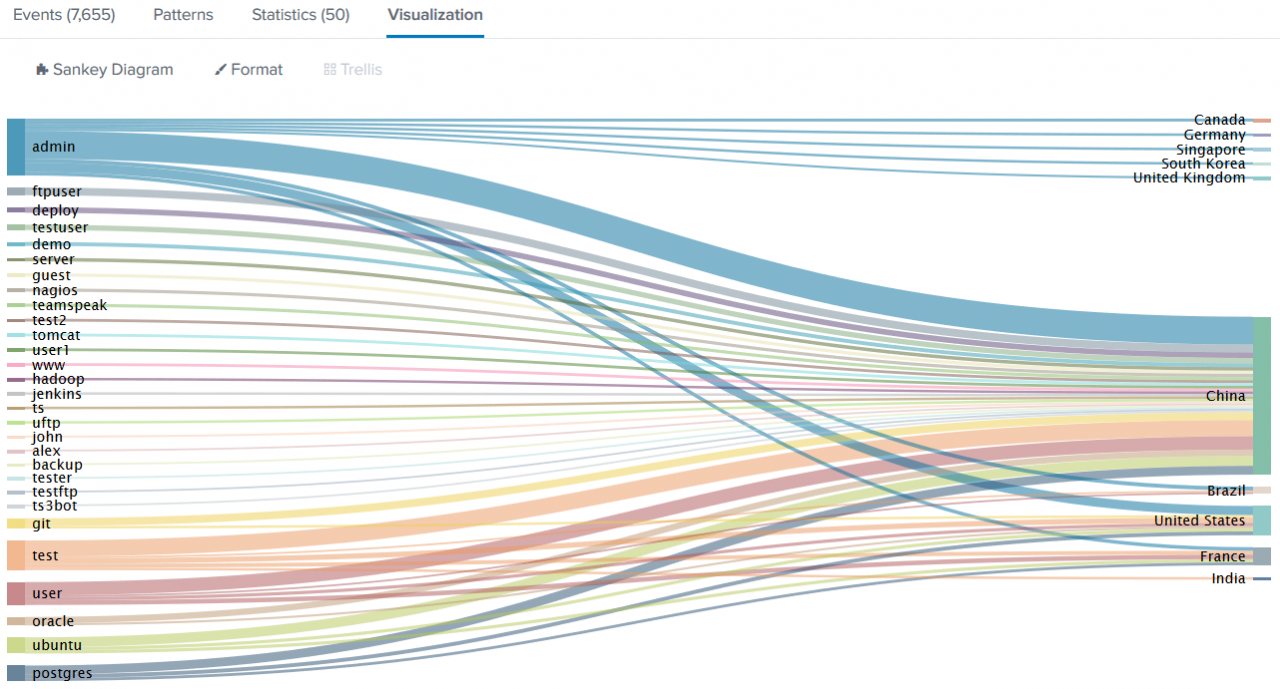
CND has various research and data intelligence initiatives to ensure that we're in the best position to support our clients and this week I delved through a sample of machine data logs and extracted the last 60 days' worth of attempted rogue login attempt usernames. I have depicted this below in the form of a Sankey diagram of 'Username attempted', Country*, Count.
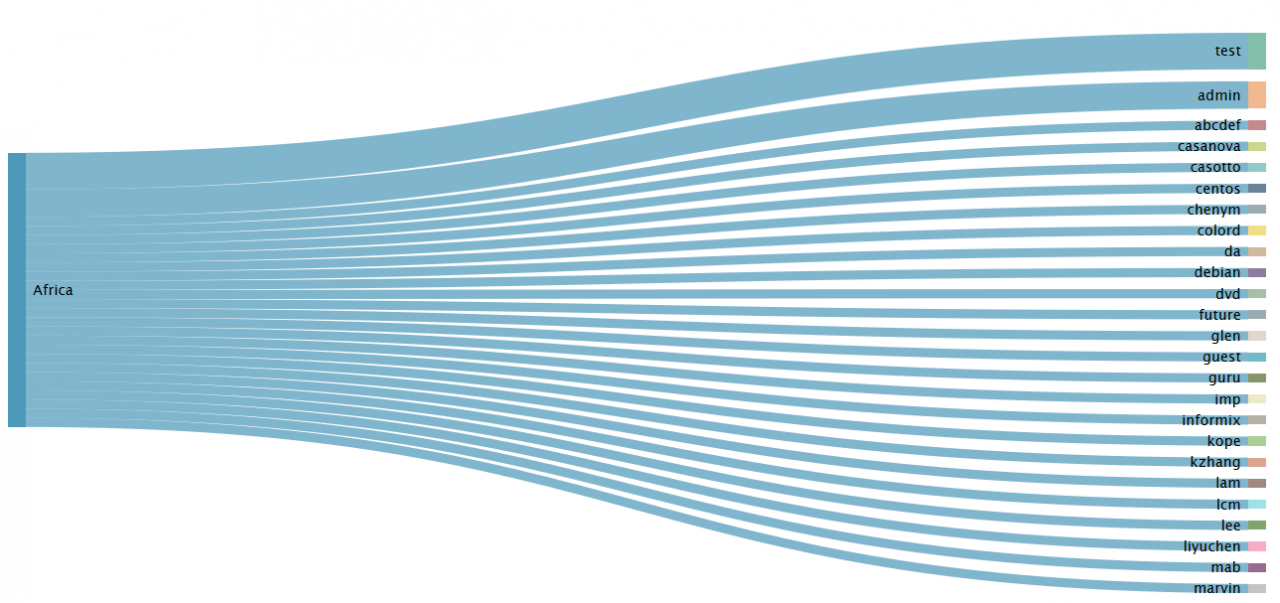
There are a few ways to split out the data and each view is revealing in itself. Below is a focus on Africa versus Asia. Looking at the Africa data you notice that there are at least 5 Chinese names and given the geopolitical influence of China in Africa there appears to be a targeting of usernames such as lee, lam, kzhang, also the *nix distro account of choice to target is centos.
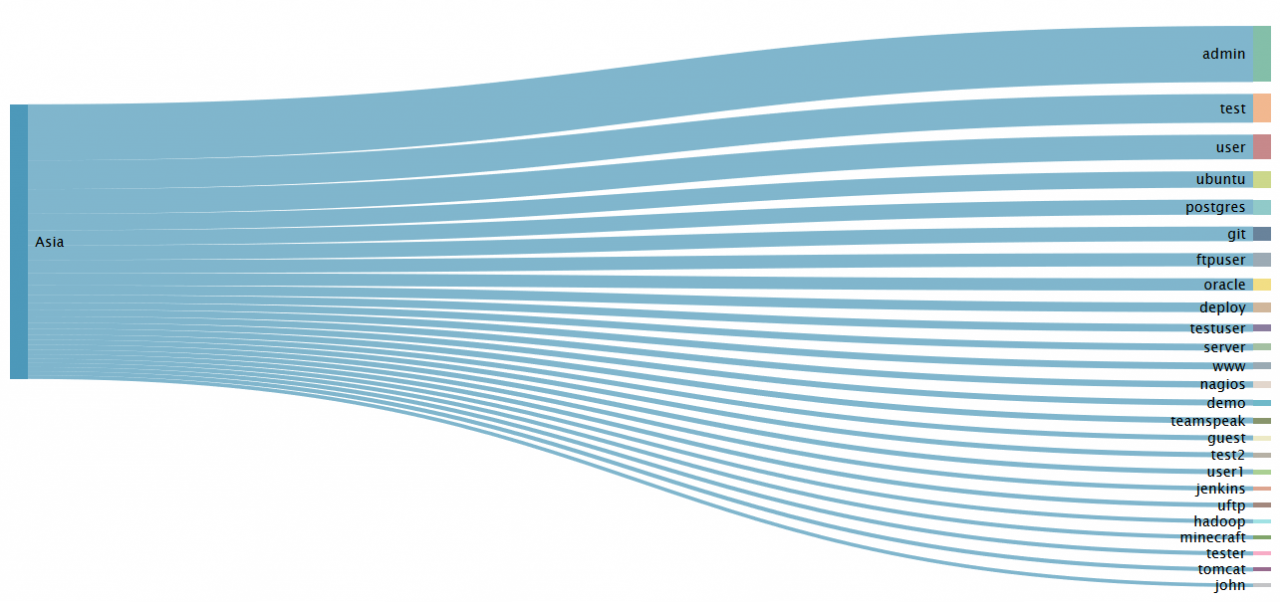
Focusing on Asia, the top attempts all appear to be focused on default accounts as opposed to individuals and that the *nix distro account of choice is ubuntu. Accepting that this is one data sample only and that a larger sample would be required to be truly statistically relevant. Regardless it is a noteworthy insight.
My key takeaways of this data sample are as follows:
- The Top 3 rogue username attempts by volume are 'admin' 'test' 'user'.
- China* is seen as the largest rogue attempt source.
- Different source countries and regions are using different usernames ranges in their attempts.
- Different linux distributions are apparently targeted from different regions.
- Over 4,800 unique usernames were seen in this data sample.
- Rogue attempts to access machines facing the internet are ever pervasive and if you're not reading your logs and understanding your exposure, you should be.
If you're concerned by this or another issue get in touch, we can help.
(*Geolocation data should be treated as implied only and not necessarily factual without verification.)