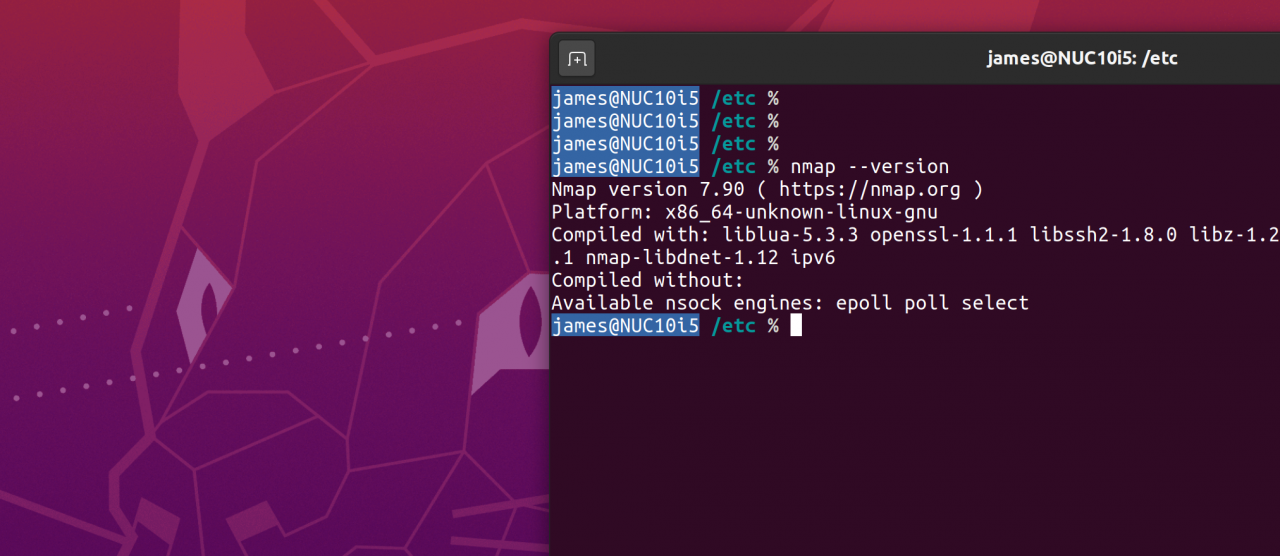
This week saw the release of Nmap 7.90 although as yet my particular Linux distro repository has yet to be updated (manual installation thus required). For security professionals it's worth reading the full release announcement here (URL), there are some significant changes and impressively the number of OS fingerprints is up to 5,678. If you've stumbled across this blog post, what this means is that hackers of all flavours from whitehat to blackhat have at their disposal a tool allowing increasingly accurate version identification of target computers including new Apple OS's. Reconnaissance is the first stage of exploitation and if a machine gives away it's OS readily through misconfiguration, unnecessary running services or inadequate hardening for it's deployment use-case then a hackers job is that much more straight-forward in the kill-chain.
Also of note and particular relevance given Covid-19 is that there are two items related to DICOM which is a standard for formats, files and communications in Medical equipment (URL). I wasn't familiar with it specifically but given how heavily targetted the medical industry has been in recent months by threat-actors this is a hotly contested battle ground and one that has been traditionally overlooked in many environments from a cyber security point of view. If you are a medical provider and have say an MRI scanner or digital x-ray machine from a popular vendor such as these models (URL) then blackhats now have at their disposal even quicker means to gain data on your patient critical appliances. Sound like scaremongering? It's worth listening to one of my favourite podcasts Darknet Diaries, episode 25 which talks through a medical provider in South America and the intriguing story behind a 'hack' (URL).
You don't have to look as far afield as South America only three weeks ago a major US fortune 500 hospital provider was impacted by ransomware (URL) and a German woman apparently died as a direct result of Malware (URL) which as my colleague recently wrote about has become an even bigger cyber threat theme this year. Furthermore if your organisation is in any way involved in the Covid-19 vaccine response then it is a surety that you will have been actively targetted and probably by APT's or Advanced Persistent Threat actors.
This might lead you to ask the question why on earth do people release tools that allow would be nefarious hackers to more easily identify vulnerable hardware on which a sick person may depend? My personal simple explanation would be that closing your eyes to vulnerabilities or putting ones head in the sand will not stop the threat from existing. Security researchers and cyber professionals are able to better serve our clients by recognising and identifying vulnerable equipment and helping segregate, isolate or protect through in depth counter measures equipment that may be targetted. Nmap is a brilliant tool and has many positive applications and appropriate deployments allow and facilitate us to help positively. Coupled with other VA or Vulnerability Analysis tools at our disposal they form the first line of scanning and review.