You've heard a great deal about ethical hackers, who emulate the Tactics Techniques and Procedures (TTP) of a hacker to test your defences. Well, I'm an ethical phisherman, I use the same TTP as an attacker to lure your staff into taking my bait and then instead of exploiting them, they receive education, whilst you receive statistics on how many staff, from which departments using what devices, at what time. This process helps to shape behaviour and encourages staff to report suspicious emails and in doing so improve your defences. Please take a look at our Managed Phishing Assessment Service https://www.cndltd.com/services/assess/phishing-assessment
Back to Basics - What is Phishing
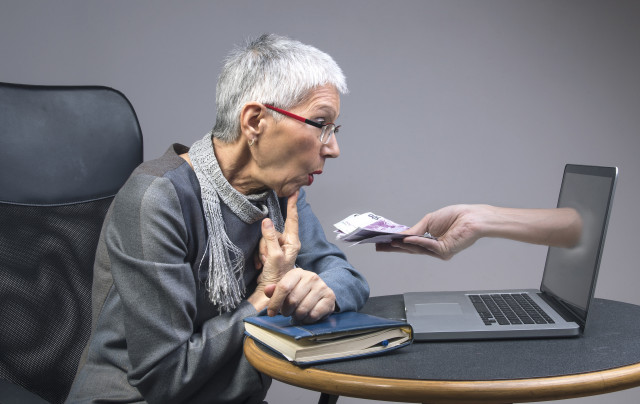
Phishing is a form of social engineering designed to target what has traditionally been seen as the weakest part of any system - the user. Phishing attacks have been around for many years and come in countless forms, complexities, and themes. From the laughable early attempts that contained broken English and far-fetched requests ('Nigerian Prince'/419 scams anyone?) right through to the well-researched, highly targeted attempts designed to closely imitate individuals and organisations.
Phishing attempts can serve different purposes; from reconnaissance and intelligence gathering through to credential theft and malware delivery. The lures used to achieve these aims are often designed to leverage basic human traits (greed, curiosity, fear etc.) to increase the likelihood of success. 'Success' could be clicking on a malicious link, opening an infected file, or inadvertently entering your credentials thinking you were logging into your Microsoft 365 account.
Attackers Do Not Possess A Moral Compass
Tactics & Techniques
Attackers are notoriously quick to take advantage of current events, topics, and situations. By rapidly adapting their tactics, techniques, and procedures they can hit unsuspecting users from fresh new angles. The current pandemic is a prime example of this. The creation of new phishing lures and malicious domain registrations took place within days of lockdown commencing and have been designed to capitalise on the fear, uncertainty, and interest in all things COVID-19. Examples include fake Virtual Private Network (VPN) updates designed to target the increased number of remote workers, and bogus HMRC and HR-themed emails looking to exploit fears associated with job insecurity and unemployment caused by the Coronavirus.
It should be realised that attackers do not possess a moral compass when it comes to launching phishing attacks. They simply do not care whether a victim is a hospital, charity, small businesses or vulnerable individual. For them, getting a result is the primary goal and this is usually some form of financial gain.
Defences - Phishing Prohibited
Thankfully, the technical countermeasures designed to filter out this type of attack have progressed markedly in recent years. Despite the impressive advances in email security, phishing attempts still manage to evade filtering solutions and slip through secure gateways into the inboxes of unsuspecting users.
Users are busy people; lots of emails, lots of competing deadlines, yet all it could take is a momentary lapse of judgement (amongst other failings in a layered security approach…) for credentials to be stolen or for ransomware to get deployed onto your network. The fact is that phishing attacks are a low overhead and get results, so they will remain a threat to individuals and organisations for the foreseeable future.
Top Tips for Defence Against Phishing
Here are 5 tips to help improve security in the fight against phishing:
- Free is good. Make the most out of the integrated security tools available in your environment. You have paid for them as part of your service so put them to good use! Commonly used cloud platforms such as Microsoft 365 and G-Suite have some great security features that will help protect your organisation against phishing attacks.
- Forewarned is forearmed. User training, while not a silver bullet, helps raise awareness of phishing techniques and encourages users to report attempts. At CND we utilise phishing simulations for internal training purposes as well as to help our clients improve their defences. The aim should be to condition user behaviour so that phishing attempts are recognised and reported. Avoid the temptation of becoming obsessed with metrics and keep the focus on the bigger picture, behavioural change.
- Spoof be gone. Domain-based Message Authentication, Reporting & Conformance (DMARC), Domain Keys Identified Mail (DKIM) and Sender Policy Framework (SPF) should be implemented to help prevent email from your domains from being spoofed.
- Simple is best. Applying a simple change like setting a rule to prepend all inbound external emails with a warning can be very effective. The warning should alert the user that it is an external email and to apply additional caution. The prepended warning message is more obvious to the user if it is in the email body rather than subject line.
- Two is better than one. Two-Factor authentication (2FA) should be set up on all user accounts where it is available. Requiring multiple authentication methods to access an account will act as a safety net should the worst happen, and a user accidently transmits their login credentials during a phishing attack.

How to Pre-Pend a Warning to Office 365 Emails - CND News and Blog