What is the Dark Web?
Before you dive into the world of the dark web it's important to understand what it is and what you might find on it. The Dark web is a section of the internet that is not indexed by your 'regular' browsers, nor can it be accessed by the generic browsers such as Chrome, Edge or Firefox and instead requires a browser such as the tor browser. For all intensive purposes it is the wild west of the internet, renowned for its criminal activity it can often turn up some unsavoury clientele from ransomware gangs to hacking groups and more.
So if the dark web is as bad as they say it is, then why would anyone want to go there unless you have criminal intent? Well the answer is simple: a large portion of what is for sale on the dark web has the potential to harm enterprises and if it can harm your organisation. You need to know about it. There are plenty of other factors too as to why you would want to connect to the dark web such as for journalism and open-source research.Disclaimer/Warning
The following information in this post is meant for purely education and informational purposes only, due to the nature of the content on the dark web your experience may differ to what is shown and you may see some very unsavoury content. You have been warned.
Connecting to the Dark Web
So we know what the dark web is and we know why we'd want to view it, but the question remains how? There are many ways that you can do this but ultimately you will require a particular browser, the 'tor browser' is one of these browsers and is probably the most common. Installing the tor browser on a production system probably isn't the best idea, for that reason you'll see numerous recommendations to install a Linux distribution of some kind in a virtual machine which isn't connected to your corporate network, this way you're operating in an isolated environment if the worst happens.
My personal preference is to go one step further and utilise Tails Linux as a bootable USB stick. The Tails linux distribution is tailored towards privacy and has a few tools pre-installed out of the box that help us connect to the dark web, the main one being the tor browser. The main attraction with Tails is that there is no persistence between sessions, as soon as you shut down the OS any files saved or programs downloaded are gone. It is worth noting that you can optionally enable persistence but it's not recommended in this use case.
Downloading and Installing Tails
Tails Linux can be downloaded from their site, https://tails.boum.org/, feel free to check out the information on the project about how Tails works and how you can use it.
The download may take a few minutes depending on your connection, but once it's downloaded you'll need to prepare the image file so that you can run the operating system from a USB stick. There are some pre-requisites here:- Firstly, a USB drive. I recommend one that is at least 8GB in capacity.
- Secondly, you'll need to write the image file to the USB drive. A tool called 'Balena Etcher' (https://www.balena.io/etcher/) will work for Windows, for Mac/Linux devices you can utilise 'DD' which is a tool built-into these operating systems.
- Finally, you'll need the image file downloaded earlier.
With these pre-requisites met the installation process is reasonably straight forward:
- Make sure the USB drive has been formatted (doesn't contain other data) and is inserted into your device.
- Open up Balena Etcher (or your tool of choice).
- Click on 'Flash from File' (If using Etcher, other tools may vary) and select the image file you downloaded earlier.
- Select the USB drive that is plugged in as the target.
- Click Flash!
After a few minutes you should now have a bootable version of Tails Linux. Ta-Da!
Running Tails
With Tails installed on a USB stick and plugged into your computer you may be wondering how to run it? Well wonder no more, essentially you need to load into your boot options when the device starts and select the USB stick. It's important to note that this may not work on devices set to UEFI-boot, or devices with Secure boot enabled. If your device has either of these options it's recommended to utilise Tails in a Virtual Machine, this way you will still have the tools required.
To get to the boot options press the relevant key when your manufacturers logo is displayed on screen shortly after pressing the power button, this will vary depending on the manufacturer so I've put together a list of some here:
- Dell, F12
- HP, Esc OR F9
- Lenovo, F12
- ASUS, F8 OR Esc
From within the boot options, use the arrow keys to highlight the USB stick and press enter, Tails should now boot. You'll be presented with a few options before landing on the desktop environment.
The Tor Browser
Searching the Dark Web
The dark web can be searched much like the normal internet or 'surface web', the main difference is that the dark web sites use a different top level domain. Instead of .co.uk or .com sites will use .onion as their domain and normally the address is a long string of alphanumerical characters. That's not to say that you can't use the Tor brower to also search clear-web sites as you certainly can, just expect the loading time to be significantly longer than your conventional browsers. More and more organisations are moving to having a presence in the dark web, mainstream sites such as the BBC or Facebook now have their own .onion addresses.
Search Engines of the Dark Web
Just like the surface web you can utilise search engines to search through the .onion addresses to find what you're looking for, however, these are somewhat unknown compared to the likes of Google or Bing. Here's a list of some search engines for the Dark Web and their .onion addresses:
- DuckDuckGo (https://duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion/)
- DarkSearch (http://darkschn4iw2hxvpv2vy2uoxwkvs2padb56t3h4wqztre6upoc5qwgid.onion/)
- Torch (http://torchdeedp3i2jigzjdmfpn5ttjhthh5wbmda2rr3jvqjg5p77c54dqd.onion/)
- Ahmia (http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/)
As a side note regarding the .onion addresses, newer v3 addresses are available and in-use by some sites, these addresses are much longer and more obscure, replacing the v2 addresses that are in-use today.
Staying Safe on the Dark Web
Whilst venturing on the dark web it is important to keep in mind the sort of content that is linked to the dark web and what you may find. It is very easy to find yourself on pages you'd wish you hadn't seen. Always be vigilant and remember to not click on adverts or links. Whilst you aren't protected by features such as 'SafeSearch' there are a few steps you can take to remain safe, the top tip being to increase the 'Security level' of the tor browser when you're searching. In the top right corner of the browser you should see the following icons:
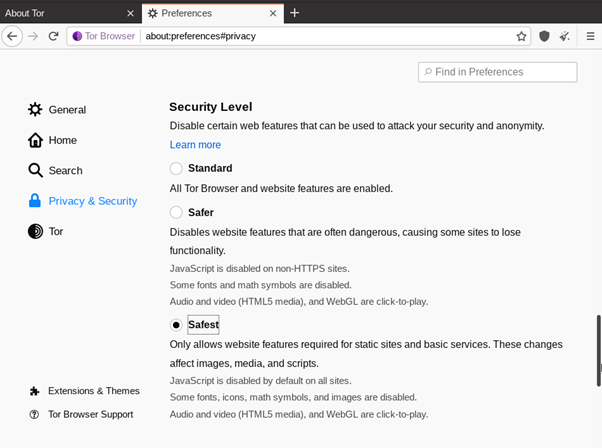
If you click on the highlighted icon and select 'Advanced Security Options' this will take you to Tor's security settings, here you can select your security level as well as other settings. It's recommended you select 'Safest' as this will ensure that all JavaScript is disabled and audio and video will not autoplay.
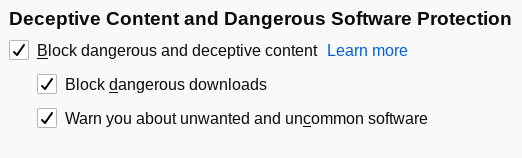
Scrolling down this page will also provide the option to 'Block dangerous and deceptive content' which can help you remain safe when traversing the great unknown.
In need of a Torch?
If you're worried the Dark web may be too dark for you then please reach out to CND. Our analysts are ready and willing to search the dark web on your behalf, providing you with the info without the risk! Get in touch today to schedule a call at